In the wake of a series of damaging cyber intrusions on private businesses controlling critical pieces of U.S. infrastructure, Harvard Kennedy School Senior Lecturer Juliette Kayyem says that countering the growing threat will require erasing the “legal fiction” that cyberattacks are different than physical attacks on American civilians.
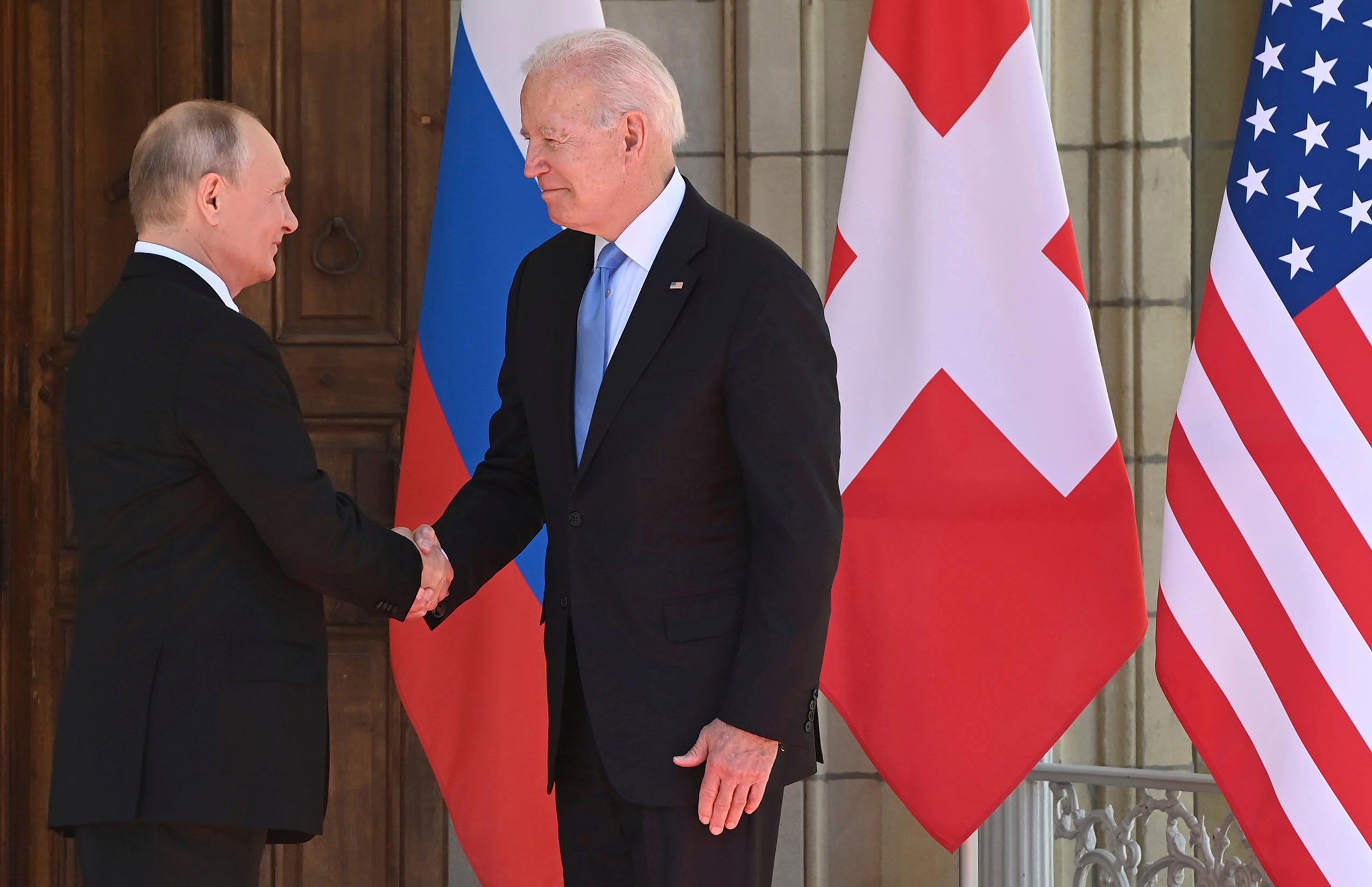
In May 2021, the Colonial Pipeline became the latest high-profile company to fall victim to a ransomware attack by criminal organizations operating out of Russia. Stretching more than 5,000 miles from Texas to New York, the pipeline supplies nearly half of the fuel consumed in 14 states and Washington, D.C. The event disrupted the flow of gasoline, diesel, and jet fuel up and down the East Coast. At a summit this June, President Joe Biden presented Russian President Vladimir Putin with a list of 16 types of critical infrastructure that, if attacked by Russian actors, would provoke a U.S. response. Within weeks of that meeting, however, hundreds of businesses across the U.S. and abroad were temporarily crippled by a ransomware attack on Kaseya, a Florida-based information technology company. The Russian cybercriminal group behind this latest incursion is also suspected of attacking JBS, the world’s largest meat processor, earlier this year, disrupting American food supplies.
A 1995 graduate of Harvard Law School, Kayyem served as Assistant Secretary for Intergovernmental Affairs at the Department of Homeland Security during the Obama Administration, is a CNN national security analyst, and is the author and editor of several books, including “Beyond 9/11: Homeland Security for the Twenty-First Century” and the forthcoming “The Devil Never Sleeps.” Harvard Law Today recently spoke with Kayyem about what the U.S. can do to deter future attacks.
Harvard Law Today: Are we in the midst of a cyber war?
Juliette Kayyem: I don’t like to call it cyber war because it puts people in the mindset that government is the only solution. Governments fight wars. We are in an epic cyber battle with different pieces, which are important to separate. There are still the traditional attacks by foreign adversaries against our government networks, including the .mil domains for the military or .gov domains for civilian federal, state, and local governments. We’ve seen that with the security clearance hacking and with other sorts of cyber intrusions. We have to do everything we can to thwart those attacks and to make it more difficult for our systems to be vulnerable. And then we need to go on offense, which often includes both overt things, such as the naming and shaming that we’ve seen going on, as well as covert activities that we don’t know about. Are we able to disrupt, say, Russia’s military network? (Russia wouldn’t admit it if we did, of course.) So, there might be all sorts of covert activities we could turn to.

I think what we’re seeing now is more complicated and reflects the nature of our homeland security structure, where two things are happening. The first is that our public infrastructure is owned by the private sector. So, an attack on our privately-owned infrastructure ends up having public consequences that are of concern to the government, whether it’s the Colonial Pipeline attack or the disruption to our food supply. So, that’s one piece. The second piece is what we call the downstream attacks, which is when cyber criminals aligned with a government attack a private entity whose downstream clients include both the private and public sector.
HLT: How do you prevent or deter these newer kinds of attacks against privately-owned public infrastructure?
Kayyem: We want to protect networks through layered defenses and cyber hygiene and all the words that we use to make ourselves safer, and to make sure that the vulnerabilities don’t exist. You want to avoid the single point of failure — the single access point that an adversary can use to get into and disrupt not just one system but downstream clients.
But we also need to assume breach. We need to be better prepared for these breaches to happen. We’ve built an entire cybersecurity infrastructure which has sold the illusion of perfect security, and we need to rethink that. We should assume there will be breaches and ask what we have done to mitigate the impact, to ensure that we have redundancies in the supply chain, and to give ourselves more options when these events occur. When the Colonial Pipeline got breached, it only had two options: to either pay the ransomware or shut the whole thing down. That’s not a sophisticated safety system. A lot of cybersecurity companies have gotten exceptionally rich selling to clients the mythology that their system can be protected and secured perfectly. But if your network is attached to anything, it’s vulnerable. And you can make it less vulnerable, or you can take it offline, which is an option, but you better also know what you’re doing after you assume breach.
HLT: How should we think about cyberattacks on privately-owned companies, and what is the U.S. government’s responsibility to intervene?
Unless we start to frame these as similar to physical attacks, their impact and significance will not be understood by the government or the enemy.
Kayyem: We have had a hands-off attitude when it comes to cybersecurity. The legal distinction between cybersecurity and physical security — which impacts how we think about governance, the way these companies hire, the way we regulate them — that distinction no longer holds. In other words, a cyberattack will, in a lot of instances, also have a physical impact. So, our laws and our regulations need to take that into account.
Think about the nuclear industry, which is heavily regulated because it is critical infrastructure and if anything goes wrong, its impact will be felt by the public. We view that as appropriate regulation over a very consequential industry. We’ve got lots of other consequential industries — electricity, water, etc. — and harm to any would have an impact on the way we live and our livelihoods. So, we need to not think of these as cyberattacks but think of them just as attacks, attacks against civilians.
HLT: How is the Biden administration addressing this question?
Kayyem: In its most recent executive order, the Biden administration is better regulating the energy distribution industry — which was impacted by the Colonial attack — by requiring a bunch of things, including more disclosure about when they’ve been hacked and more response planning so that you don’t have this on/off switch situation that Colonial faced. The order also pushes companies to get different cyber systems so administrative processes like billing and HR are on one network, but the network that’s protecting the delivery of the energy is on another, so one is more porous than the other. So, they’re trying to do it at least through one industry, but we need to do it across all critical infrastructure, and get rid of this legal fiction of a difference between physical and cyber security.
However, there’s something more than the legal fiction between cyberattacks and physical attacks. I think the industry has cultivated this idea of specialty as well. In other words, they’re very much invested in treating themselves as cybersecurity specialists, as unique and pristine and, in some ways, unregulatable. And that’s just not true.
HLT: The U.S. has endured a series of attacks by state and non-state actors, often acting at the behest of a state. What would the U.S. government have done differently if Russia had physically harmed the Colonial Pipeline, for instance?
Kayyem: Unless we start to frame these as similar to physical attacks, their impact and significance will not be understood by the government or the enemy. But that doesn’t mean that the tools to respond are the same. We’re not going to war with Russia over the Colonial Pipeline. And the military, more often than not, should not be a resource for responding to these types of attacks. It’s just not the appropriate framing on the response side.
There are a number of other tools at our disposal. These include the traditional sanctions and legal tools — naming and shaming does work, legal prosecutions work, sanctions, disrupting the money flow to these criminal enterprises or their access to the internet. There is also the option of covert action. So, there are four or five tools that we can still use that do not get us to “war.”
Ransomware is the tool of a very weak leader. Ironically, while it is disruptive and chaotic, it also is a clear sign of Putin’s limited strength.
The other reason why the tools are different is that a lot of this is being done by government-aligned or government-approved criminal enterprises, but can’t be directly attributed to the countries themselves. So, we want to be careful. I think [President] Biden has been really smart and that he is not just saying ‘Russia, Russia, Russia.’ He’s buying himself some time for both overt and covert actions. We are the United States, so we do take more seriously any efforts that would impact civilians, both as a legal matter and as a moral matter. The idea that we’re going to go after Russia’s water systems or its electrical grid… we don’t do that casually. I know a lot of people like to talk tough, but we just have to realize that the tools to respond are going to be different. They’re more difficult and less transparent, but we need to have the mindset that these are attacks, and calling them cyberattacks doesn’t make them any less so.
HLT: What is Vladimir Putin trying to accomplish through these attacks?
Kayyem: Chaos. He’s a weak man leading a weak country. His strength is in the exertion of power. He can’t do that militarily, he can’t do that economically, but he can do that through disruption. So, his master plan, as it was with the elections, is just to mess with people’s heads and to highlight our vulnerabilities. He’s not making money off of this ransomware; they’re only asking for a couple million so companies will be willing to pay, so it’s not much. This is all about his assertion of strength through chaos. Compare that with China. China’s assertion of strength is through economic, geopolitical, and military assertions of that strength. They’re also doing cyberattacks, but they don’t need pesky ransomware to show their strength. To put it more succinctly: Ransomware is the tool of a very weak leader. Ironically, while it is disruptive and chaotic, it also is a clear sign of Putin’s limited strength.
HLT: Are there historical precedents for these kinds of attacks by non-state actors tolerated or sponsored by a state and, if so, how did those cases work out?
Kayyem: Think about drug cartels. The reason why this is happening from Russia or aligned with Russia is because those groups feel confident that they will suffer no consequences. The same was true with the major drug cartels in Colombia, which were able to thrive because the government was basically purchased. There’s not going to be a simple solution to dealing with that, but I think that’s the way to think of it. One of the tools we do have is to go after the funders. All of these private militias and mercenaries, as well as Putin’s oligarchs, are supported by an apparatus that likes their money. And the Biden administration is asking themselves what, beyond sanctions, will hurt the money people and make it not worth it for them. And I think that’s going to be one solution as well.
The thing I do want to make clear is the public clamoring for a response is important, and I think there are overt responses, including the naming and shaming, the international support for us, and the prosecutions. A lot of these prosecutions and investigations are multi-country. The United States just did a big disruption in the Ukraine with South Korea and Ukraine. That’s a pretty unique combination of countries because we were all impacted by this ransomware group. And again, there are covert activities that are available to the U.S. government that we may never know about. These are likely to include disruptions may never become public. But it is our way of saying “if you want this to really hurt, we can make it really hurt.”